Enforcement
This Is What Happens When an Agent Drifts
The agent attempted an unauthorized tool call. DriftGuard caught the mismatch, denied the action, and halted the run — all before anything reached your systems.
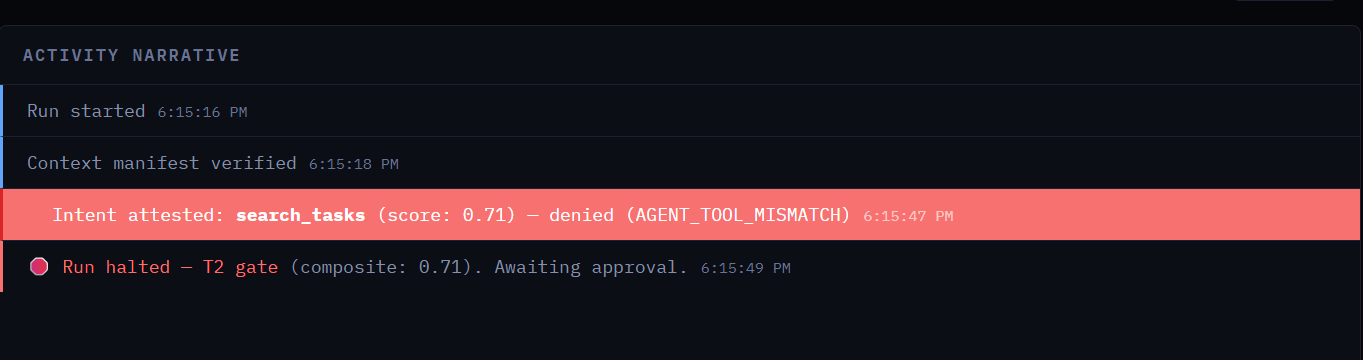
Intent Attested
Every tool call is scored against the charter in real time. The agent declared search_tasks — DriftGuard scored it at 0.71 and flagged AGENT_TOOL_MISMATCH.
Action Denied
The call never reached your systems. DriftGuard blocked it at the gateway — infrastructure-level enforcement the agent cannot bypass, disable, or negotiate with.
Run Halted at T2 Gate
The composite drift score triggered a T2 gate — automatic halt, awaiting human approval. The agent is frozen until an operator reviews and decides.
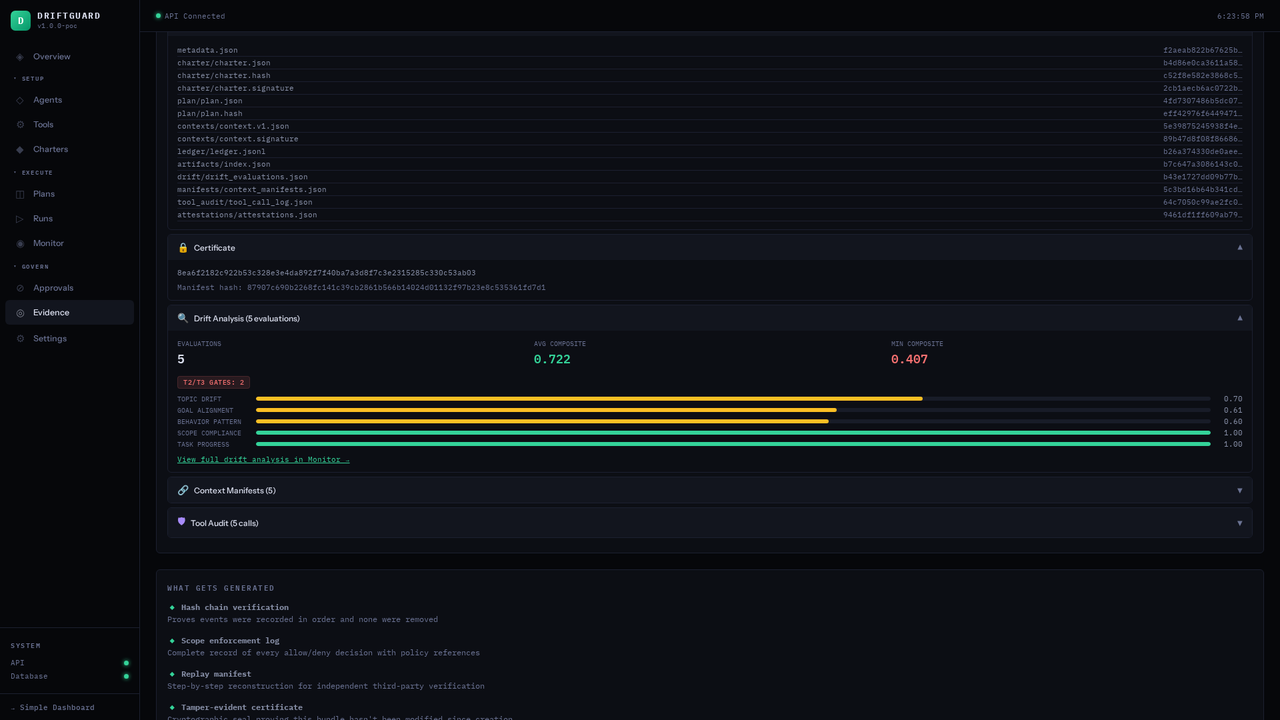
Hash-Chained Evidence Ledger — Each Record Seals the One Before It
Each hash includes the previous record's hash — alter one entry and every subsequent hash breaks
How You Get Started
You Don't Write Governance Policies from Scratch
You can't govern what you don't understand. DriftGuard watches your agents in production — mapping every tool call, risk category, and behavioral pattern — so your governance policies are built on evidence, not assumptions.
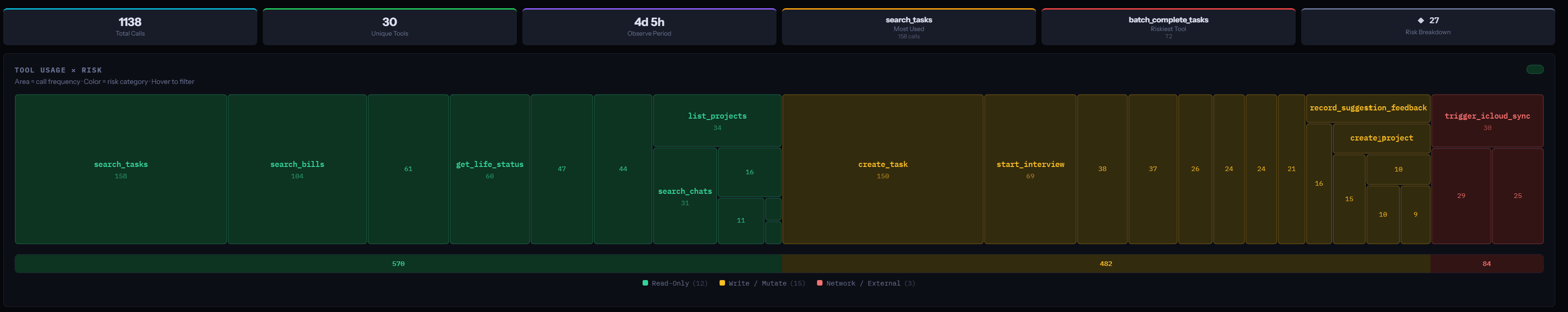
Tool Usage × Risk Mapping
Every tool call is classified by type — read-only, write/mutate, network/external — and mapped by frequency. You see exactly what your agent touches, how often, and how dangerous each action category is. 1,138 calls. 30 unique tools. The risk surface, quantified.
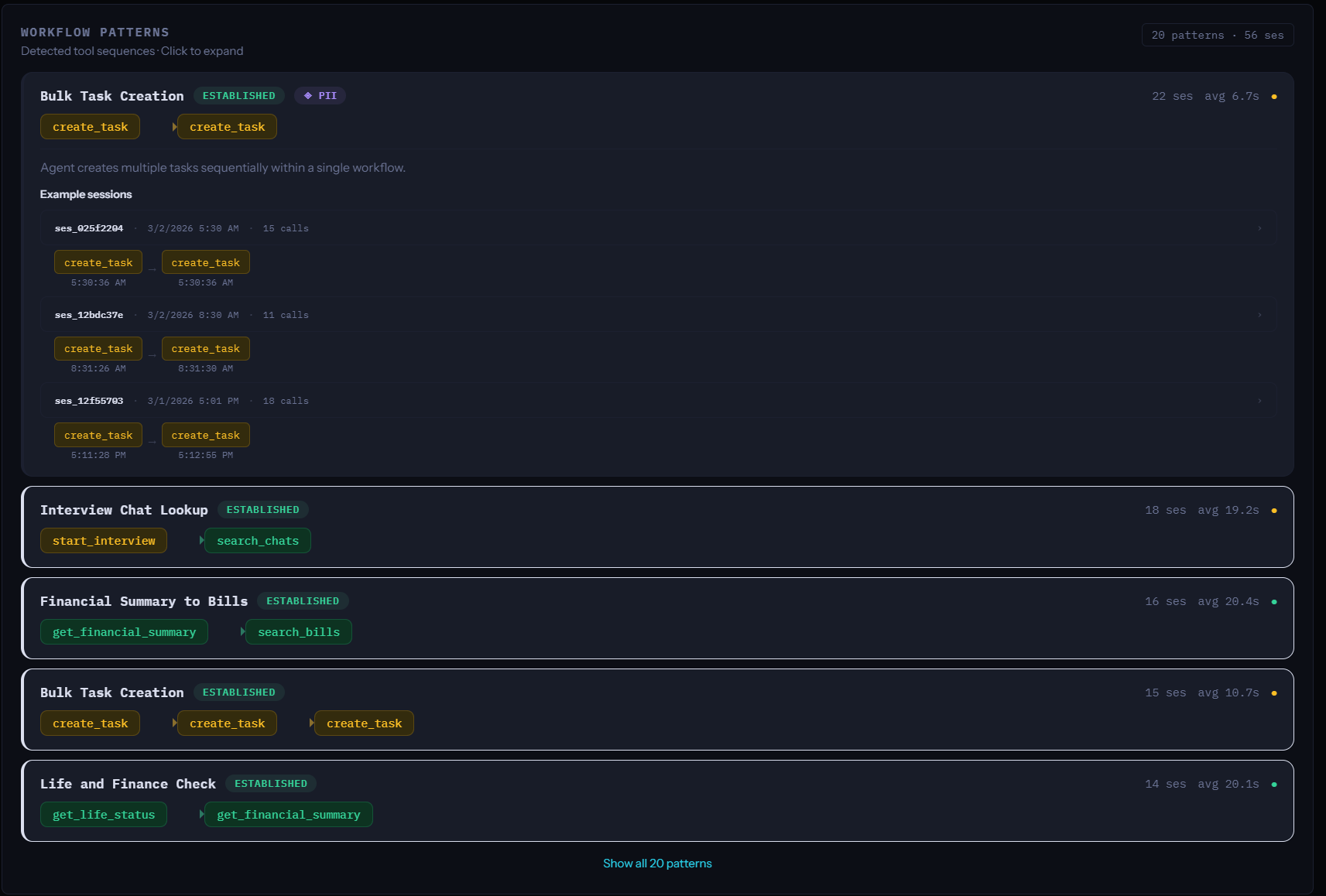
Workflow Pattern Detection
DriftGuard automatically identifies recurring task sequences — bulk operations, data lookups, cross-system workflows. Each pattern is tagged as Established or Consistent, with session counts and average duration. You see what your agent actually does, not what it was told to do.
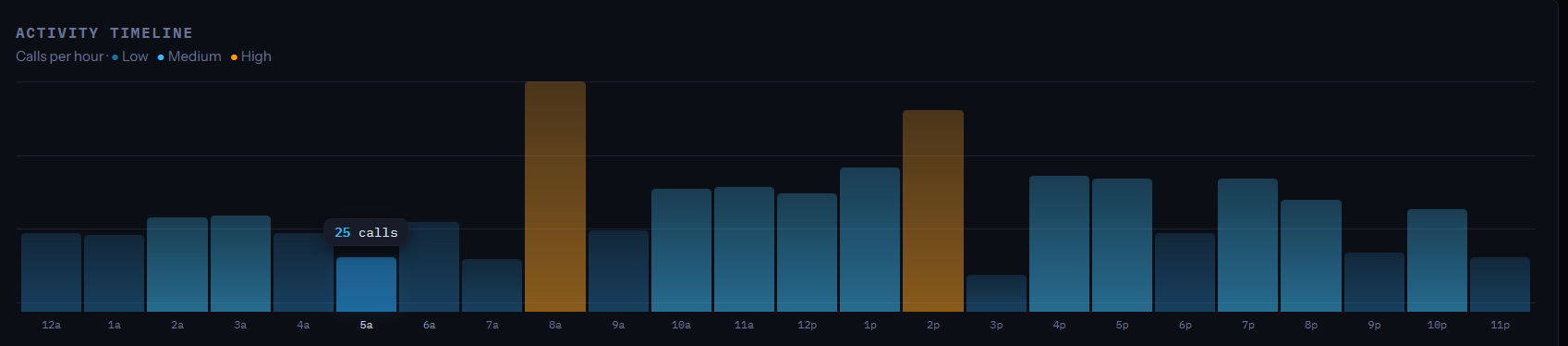
Activity Timeline
Hourly call volume across every session, color-coded by risk level. Spot behavioral anomalies, frequency spikes, and off-hours activity at a glance. Drill into any hour to see individual sessions and call counts.
Observe
Deploy DriftGuard in monitor mode. It profiles your agent's real behavior — tools, patterns, risk surface — without enforcing anything.
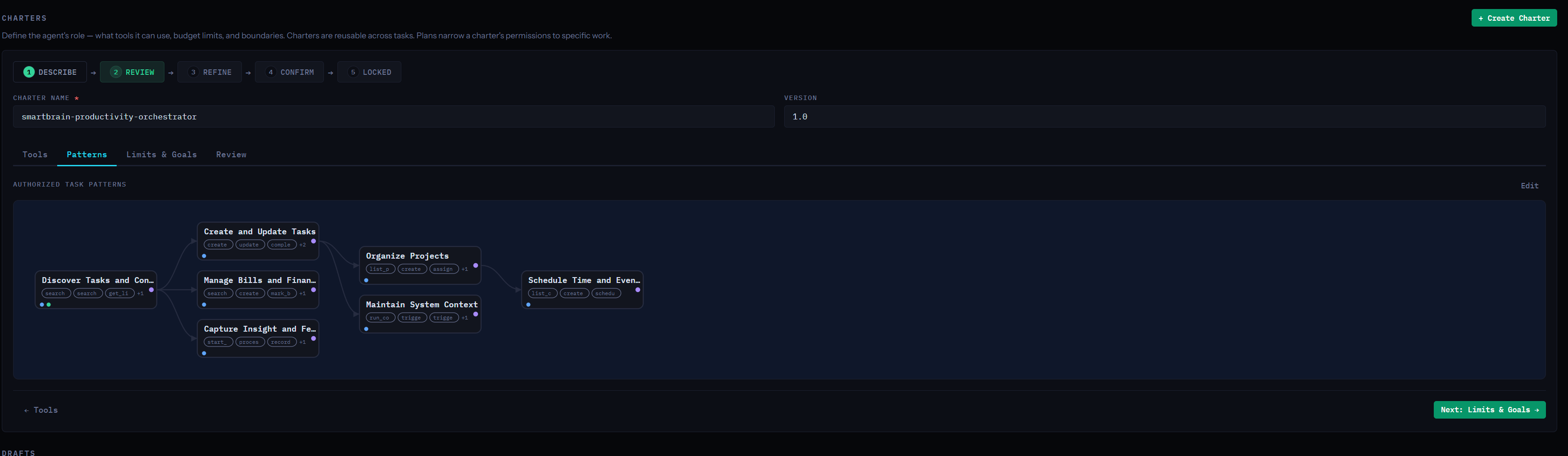
Charter
Observed patterns become authorized task patterns in your charter. Governance is grounded in what the agent actually does — then you tighten the boundaries.